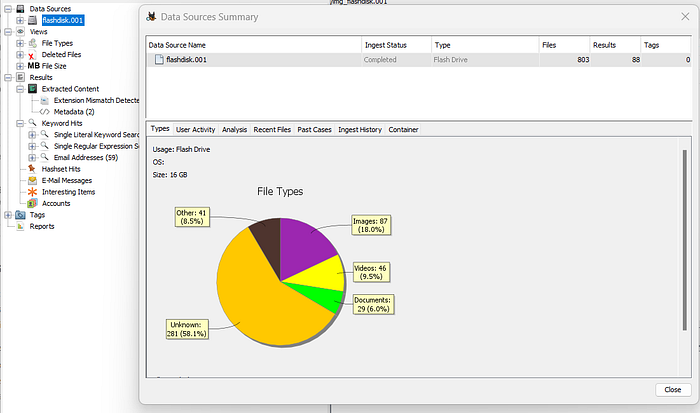
Scenario: We found a flashdiks on the road. Then we tried to investigate using FTK Imager and Autopsy.
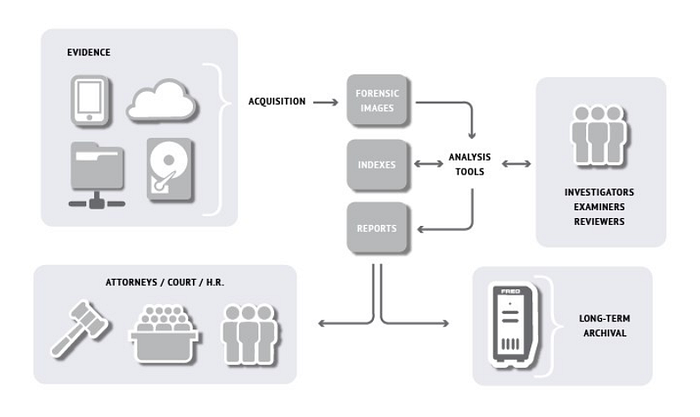

# Case Evidance Steps:
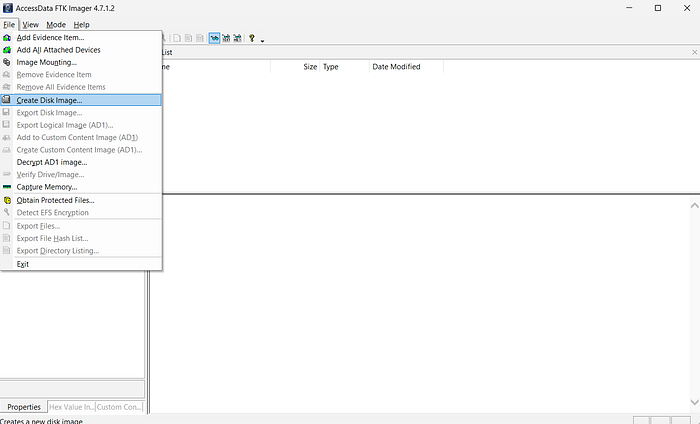
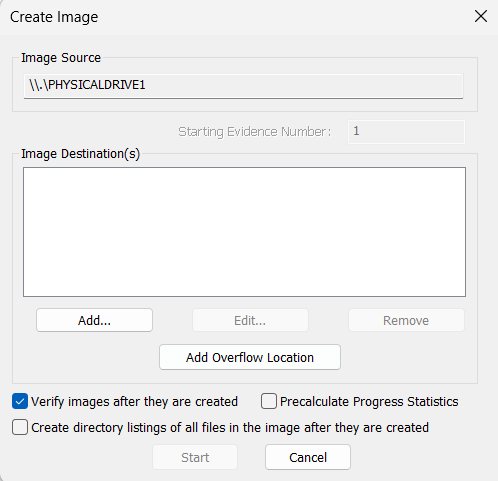
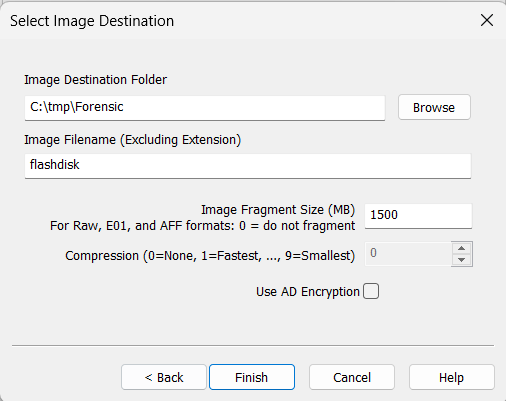
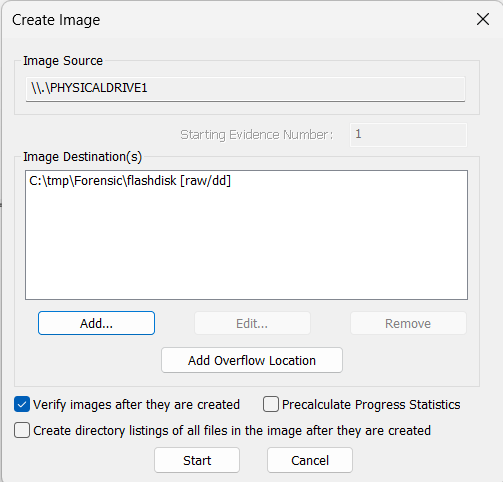
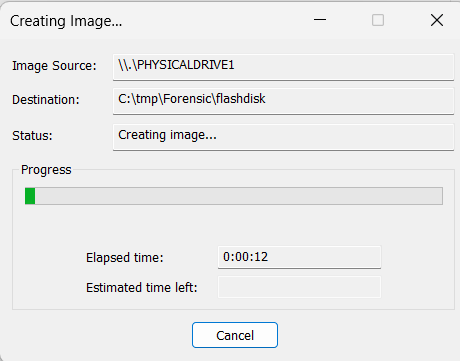
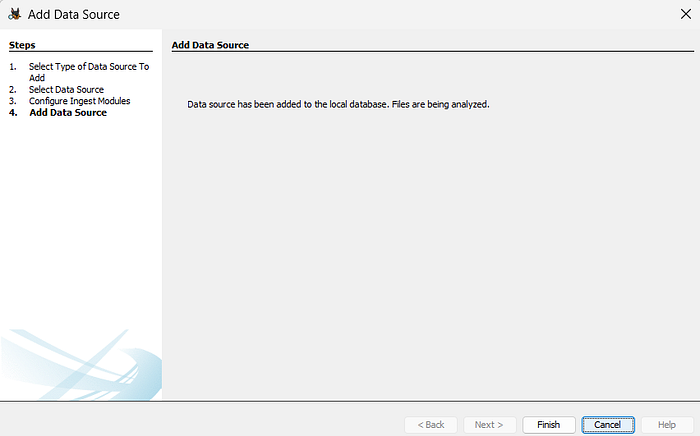
1. Create Image using FTK Imager
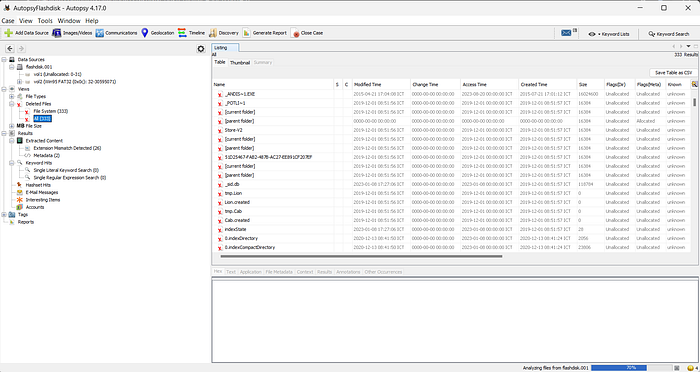
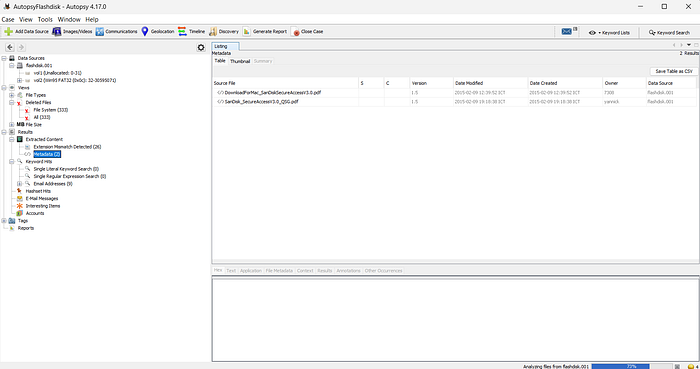
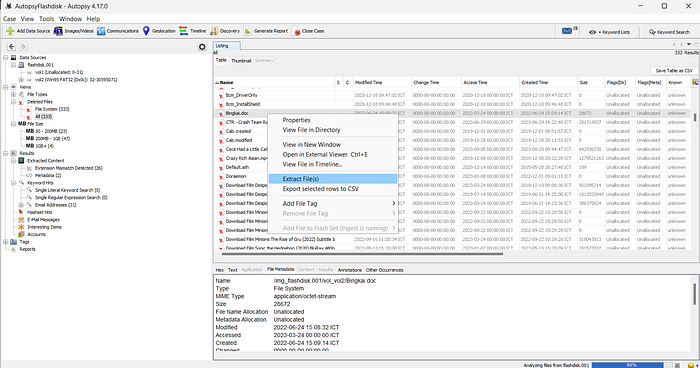
2. Analysis Image using Autopsy
# Download
1. FTK Imager: https://www.exterro.com/ftk-product-downloads/ftk-imager-version-4-7-1
2. Autopsy: https://github.com/sleuthkit/autopsy/releases/download/autopsy-4.17.0/autopsy-4.17.0-64bit.msi1. FTK Imager
FTK Imager is a tool for previewing and creating images that we can use to test digital evidence. FTK imager can also do a perfect copy (forensic image) without changing the data or metadata of the original evidence.
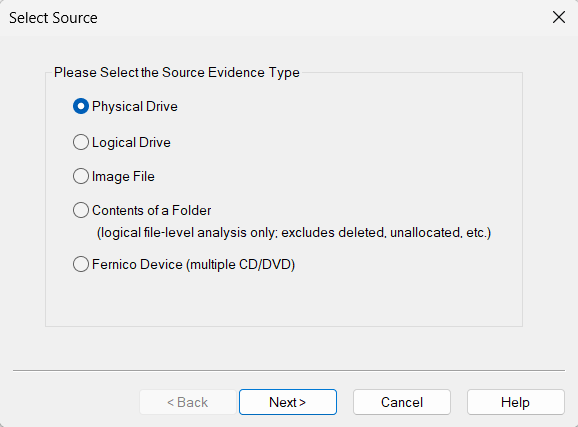
# Explanation:
- Physical Drive, for sources sourced from internal or external storage which will then be imaged as a whole from the storage.
- Logical Drive, for sources sourced from storage directories. For example, only imaging Local Disk C: / or Local Disk D: / and not the entire storage.
- File Image, for sources that come from a single file that is then imaged.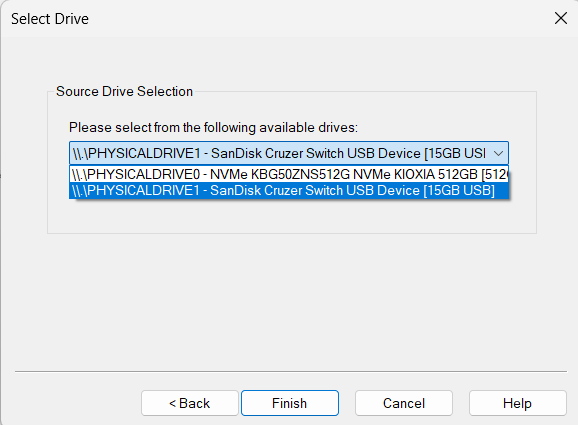


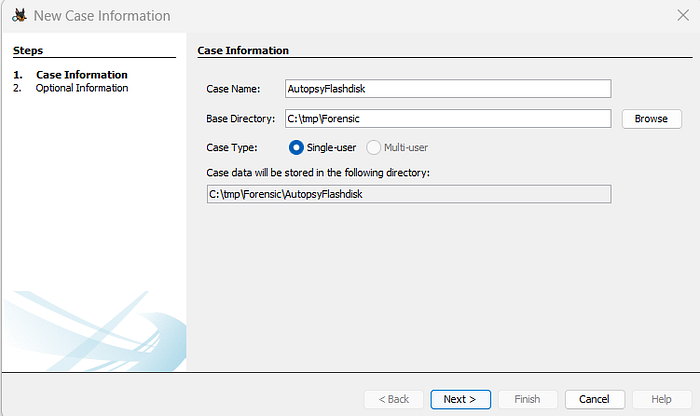
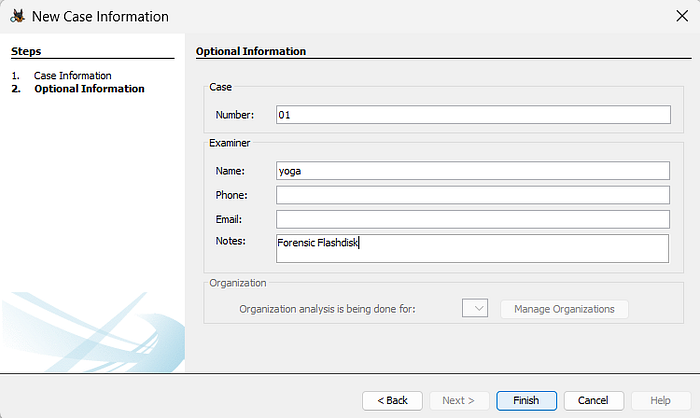
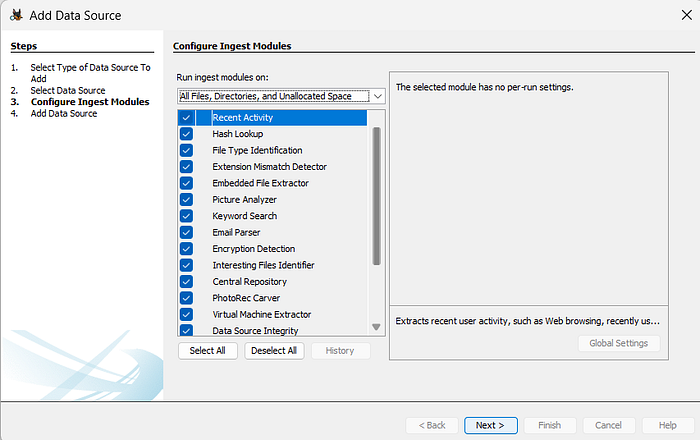
2. Autopsy
Autopsy application is an open source forensic platform that is easy to use, and is able to analyze all types of mobile devices as well as those of you who use PCs and laptops. The Autopsy application can run and be used on Operating Systems that use Linux and Windows. Autopsy application is an application that can find out hidden information from a file, starting from when the file was created, when the file was last changed, when the file was last accessed, when the file was deleted, this application uses what encryption, and what password.

# Explanation:
- Disk Image, for files that have the *raw, *bin, *img, *e01 extension.
- Local Disk, for sources taken from the local disk of the connected device
- Logical File, for one specific file only

3. Conclusion
From the autopys results above, we can get some files that have been deleted before. By using these two applications, we can try some of the advantages of the application, one of which is finding lost files. Because every file or data that has been deleted will not always just disappear, there is a possibility that artifacts of a file or data are left behind.